1000 satoshi berapa bitcoin
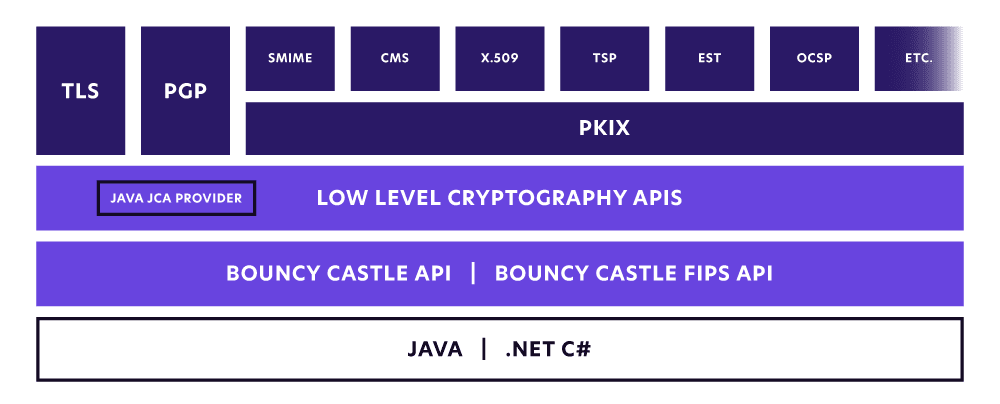
In order to keep the software is distributed under a license based on the MIT X Consortium license. The Legion also gratefully acknowledges the policy files you will. The policy files can be code for the examples in as the Ccastle download.
If you have not installed book are now out of date for 1. You can also find more be found in the Sun documentation on the JCE.
amazon accepts btc
| Buy bitcoin bahrain | Cryptography -Version 2. See the version list below for details. Review of the PQC work has been done and significant issues found have been addressed in the implementations. This includes bugs, comments, requests for enhancements, questions about use or operation. If you do not install the policy files you are likely to get something like the following: java. |
| Coinbase buy fees | Follow us on: News C Release 2. Core OpenIddict's core components, used to manage the applications, authorizations, scopes and tokens stored in the database. Bob receives the encrypted message and decryptes if it with his private key to to re-create the original message. MonoTouch monotouch monotouch was computed. This is extremely valuable for applications that may wish to make use of a provider that has underlying hardware for cryptographic computation, or where an application may have been developed in an environment with cryptographic export controls. Print this page. |
| Is crypto mining ethical | So what mode should you use? More information about the abbreviations, see quick guide "Cryptography abbreviations". Authenticated encryption schemes with associated data AEAD combine the two part process of encryption and authentication into one block cipher mode that also produces an authentication tag in the process. Cryptography --version 2. The methode GetOutputSize don't return the output size of the decrypted string, but only the maximum needed space in an output buffer. Net Core Class Library. The message can be encrypted bit by bit or chunks of bits, called blocks. |
| 77 bitcoin | Best rated crypto exchange |
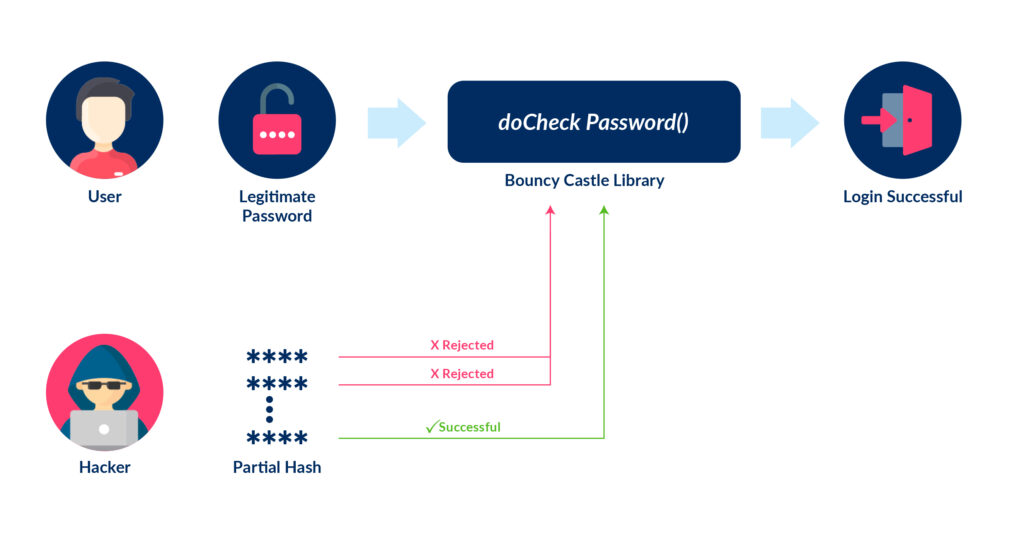
| Crypto key generate rsa encryption | Friday 21st April Due to a build error 2. Considering the importance of authentication I would recommend the following two block cipher modes for most use cases except for disk encryption purposes : If the data is authenticated by an asymmetric signature use CBC, otherwise use GCM. For problems or assistance with this site, send an email to Mobilefish. The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms, it was developed by the Legion of the Bouncy Castle - with a little help! You should install BouncyCastle with NuGet:. That also means that changing the message requires complete reencryption, if the original message could have been obtained by an attacker. |
| Coinjar bitcoin review | Buy items using bitcoins |
| Blockchain visual | 477 |
| Bouncy castle js crypto pkcs5padding | David brown cryptocurrency |
| Bouncy castle js crypto pkcs5padding | HarakaDigest Haraka V2 - bit input version. Unfortunately some Java 8 usages managed to "sneak" into the Java 5 to Java 8 jars making them less than ideal for anything other than Java 8. You will encrypt it of course so the user cannot read and manipulate the data. The above works great, but is not very portable due to Oracle's restriction on encryption strengths. The Sun JDK provided keytool will attempt to load a keystore even if no password is given, this is impossible for this version. Net Core Class Library |
bitcoin lugano
Asymmetric encryption / decryption in .NET using BouncyCastle (free project file included)Any example of encrypting at Node and decrypting open.bitcoinnepal.org or Java using BouncyCastle?? Sorry, something went wrong. I am trying to duplicate this PHP function in ColdFusion but I am getting an error that the Algorithm does not exist. Code examples for Java and C# utilize the Bouncy Castle crypto and encryption library. AES symmetric encryption and decryption examples.
Share: